As a history major and creator of a contextual citation system, I’ve come to the realization how many famous quotations are passed down without access to the surrounding context.
Quotes Divorced from their Context
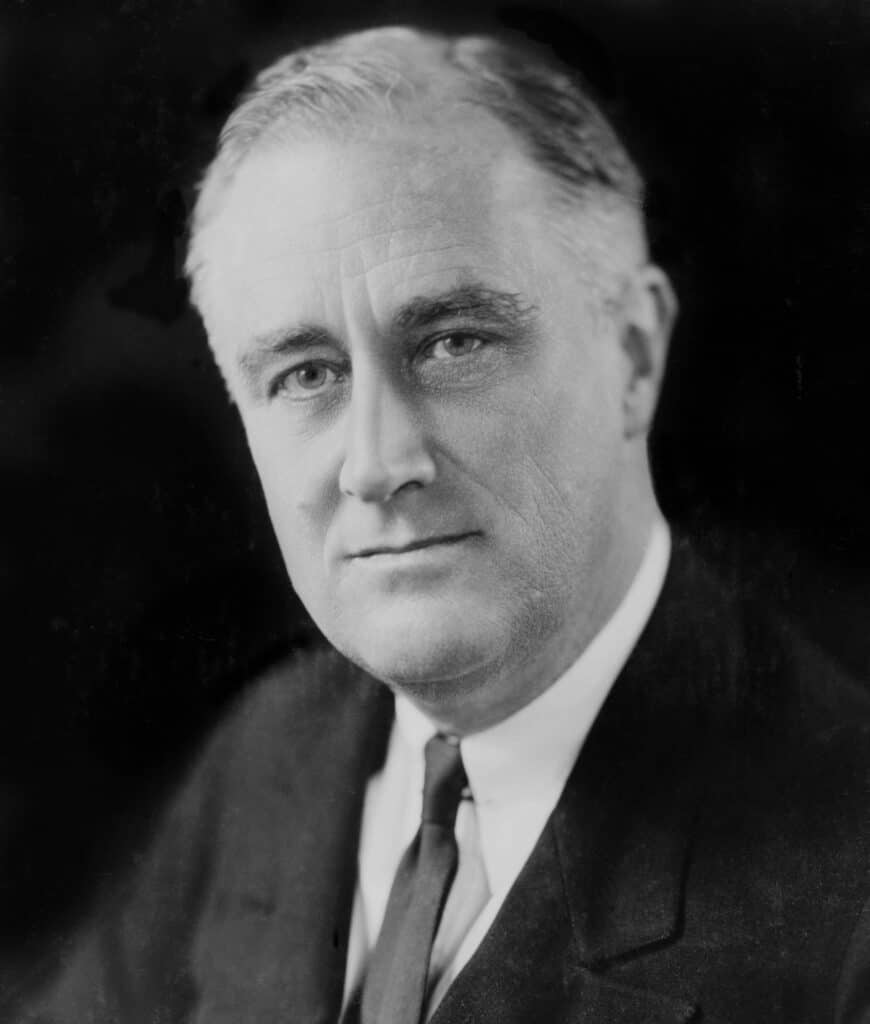
He’s a quote from FDR that we do have the context for:
the only thing we have to fear is fear itself
But go to any of the major quote websites and see how many quotes have been divorced from their original context.
- “Be yourself. Everyone else is already taken.” attributed to
- “A room without books is like a body without a soul” attributed to
- “Always forgive your enemies; nothing annoys them so much.” attributed to Oscar Wilde
For lack of a better term, I call these “naked quotations“.
These show up in journalism and on Wikipedia where we frequently have to settle for the citation of a naked quote.

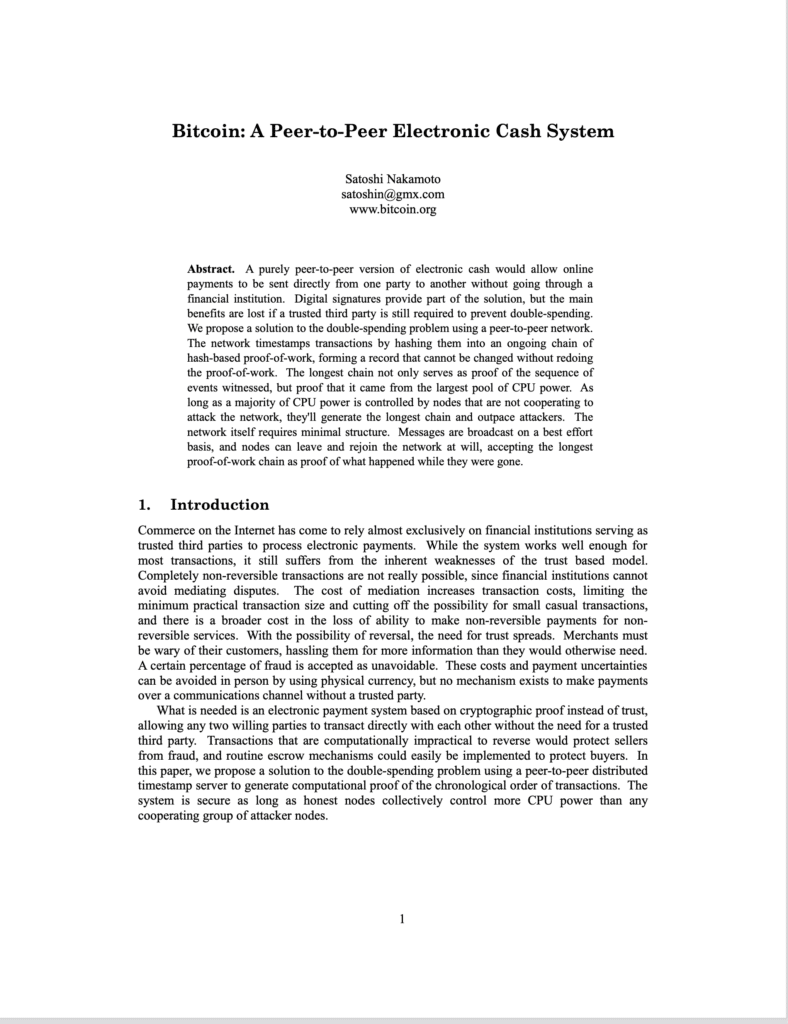
Back to Ted Nelson’s Original Vision
As part of an effort to build the trust of our readers, I encourage authors to live to a higher standard by fully citing sources and providing their readers with context.
Ted Nelson’s original vision for hypertext kept quotes connected to their sources with two-way links.
My CiteIt.net project is a rather hackish way of getting back what was lost with the web, towards Ted’s original vision.